In today’s increasingly digital world, businesses rely on robust, secure solutions to protect sensitive data. Google Workspace Client-Side Encryption (GWS-CSE) offers an added layer of protection by allowing organizations to encrypt their data before it reaches Google’s servers. While GWS-CSE ensures enhanced security and control, it requires an “External Key-encryption Service (KACL)” to be implemented by the customer.
Introducing GarbleCloud’s KMS (GC-KMS) for GWS-CSE, a powerful KACL service that is built to meet GWS-CSE’s KACL specifications. Along with the core KACL specs, GC-KMS provides administrators with advanced features that make encryption-key lifecycle management, sharing-permissions management, and security audits a breeze. With GC-KMS, organizations can have complete control over their encrypted data, ensuring only authorized users and domains have access while maintaining compliance with security regulations.
This article will delve into the various admin features of GC-KMS for GWS-CSE. As we progress, we will examine how each component complements GWS-CSE to provide unparalleled security and control for your organization’s sensitive information. Our discussion will cover the following:
- Dashboard for access tracking
- Advanced permissions management
- Flexible key management
- Extensive audit logging
- Lockdown mode for emergency response
By the end of this post, you will gain insights into how GC-KMS elevates the security and control of GWS-CSE, empowering businesses to protect their valuable data with confidence and ease.
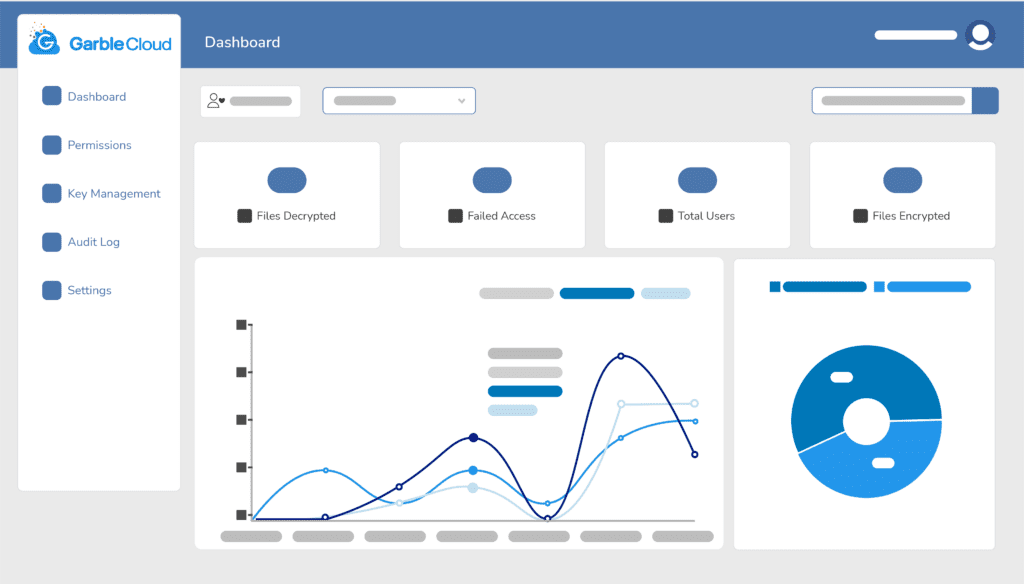
A crucial aspect of maintaining a secure environment is the ability to monitor and track access to encrypted files and documents. GC-KMS for GWS-CSE offers a comprehensive dashboard feature that enables administrators to gain real-time insights into accessing and using their organization’s encrypted data.
The DASHBOARD provides a user-friendly visual representation of the access patterns within the organization. It displays critical metrics such as the number of encrypted files, the volume of encryption and decryption events, and the most active users, among other valuable data points. This information enables administrators to identify trends, detect anomalies, and make informed decisions regarding access management and security policies.
In addition to these high-level metrics, the dashboard allows for more granular monitoring. Administrators can filter the data by specific users, departments, or time frames to better understand individual access patterns. This fine view is instrumental in detecting unauthorized access or identifying users requiring additional training on security best practices.
The dashboard feature in GC-KMS complements GWS-CSE by providing an additional layer of visibility into the encrypted data. While GWS-CSE ensures that your organization’s data is encrypted before it reaches Google’s servers, GC-KMS dashboard offers a centralized location to monitor and manage access to this encrypted information. This integration enables a seamless user experience and allows organizations to harness the full power of both tools to enhance their data security posture.
Effective Permissions Management is a critical component of any robust data security strategy. GC-KMS for GWS-CSE offers an advanced permissions management system that allows administrators to exercise granular control over access to encrypted files and documents. This level of control ensures that only authorized users and domains can access sensitive information, further enhancing the security of your organization’s data.
The permissions tab in GC-KMS provides two critical options for access control:
- Whitelisting individual users: Administrators can grant specific users access to encrypted files and documents by adding them to a whitelist. This feature enables fine-grained control over who can access particular data, allowing admins to assign permissions based on an individual’s role, responsibilities, or other relevant criteria.
- Whitelisting entire domains: For organizations that need to grant access to a larger group of users, GC-KMS allows for domain-level whitelisting. By adding an entire domain to the whitelist, admins can quickly provide access to all users within that domain, streamlining the permissions management process.
GC-KMS offers customizable permission levels, enabling administrators to define the exact level of access granted to each user or domain. Permission levels can be tailored to meet your organization’s specific needs, ensuring that users have the appropriate access rights to perform their tasks without compromising data security. In addition, permissions can easily be revoked, allowing administrators to adapt to changing security requirements and quickly remove access when needed.
One of the core components of a strong encryption strategy is the effective management of encryption keys. GC-KMS for GWS-CSE features a flexible key management system that simplifies managing and rotating the master encryption keys while ensuring the highest level of security for your organization’s data.
The KEY MANAGEMENT tab within GC-KMS allows administrators to rotate the master encryption key at their discretion. Regularly rotating the master key is a best practice in encryption management, as it reduces the risk of unauthorized access or breaches due to compromised keys. With GC-KMS, administrators can update the master key ad-hoc or set a custom interval every 30, 60, 90, 120, or 180 days. This flexibility allows organizations to align their key management practices with their specific security policies and industry requirements.
In large organizations with numerous users and complex data management requirements, having a detailed and comprehensive AUDIT LOG is crucial for maintaining security, compliance, and transparency. GC-KMS for GWS-CSE includes an extensive audit logging feature that records every action taken on encrypted files and documents, providing administrators with valuable insights and a complete audit trail.
The importance of detailed audit logs in large organizations cannot be overstated. Audit logs allow administrators to monitor user activity, identify potential security threats, and maintain compliance with various regulatory and industry requirements. Organizations can quickly respond to incidents, conduct thorough investigations, and implement remediation measures when necessary by having a record of every action taken.
GC-KMS audit logs capture a wide range of actions, including:
- Encryption and decryption events: By logging each encryption and decryption action, administrators can track access to sensitive information, monitor user behavior, and ensure that data is being accessed only by authorized personnel.
- Permission modifications: The audit log records any changes made to permissions, allowing administrators to maintain oversight of access control and ensure that the appropriate users and domains have access to encrypted data.
- Master key changes: When the master encryption key is rotated, the audit log records this action, providing a transparent record of key management activities and ensuring the highest level of security for encrypted data.
In addition to the actions taken, each audit log entry includes essential information such as the user who performed the action, the timestamp of the action, and the affected file(s). This level of detail is invaluable for large organizations that must clearly understand their data landscape and access patterns.
The extensive audit logging feature in GC-KMS enhances GWS-CSE’s security capabilities by providing a comprehensive record of all activities related to encrypted data. When paired with GWS-CSE, GC-KMS audit logs offer additional visibility and control, empowering large organizations to safeguard their sensitive information while maintaining regulatory compliance.
In a security breach or any other emergency, organizations must be able to quickly and effectively respond to mitigate potential damage. GC-KMS for GWS-CSE includes a powerful LOCKDOWN MODE feature that enables administrators to immediately cease all actions on encrypted files and documents, providing an essential ‘emergency brake’ for limiting the spread of a breach.
Lockdown mode can be activated with a single click within the GC-KMS interface, ensuring administrators can rapidly respond to potential threats. When lockdown mode is enabled, all encryption, decryption, and permission management actions are halted, effectively preventing unauthorized access to sensitive data and limiting the scope of a breach. Additionally, lockdown mode can serve as a valuable tool during planned security maintenance or system updates, providing administrators with the control needed to maintain a secure environment.
In conclusion, GC-KMS for GWS-CSE offers a comprehensive suite of features to enhance the security and control of your organization’s encrypted data. From the real-time dashboard and advanced permissions management to flexible key management, extensive audit logging, and lockdown mode, GC-KMS works seamlessly with GWS-CSE to provide a robust and powerful security solution for businesses of all sizes.
Take advantage of the opportunity to safeguard your organization’s valuable information and maintain a secure data environment. Book a demo today to discover the full potential of GC-KMS for GWS-CSE and learn how this powerful combination can elevate your data security strategy to new heights.
Book a Demo